 Facebook
Facebook
 X
X
 Instagram
Instagram
 TikTok
TikTok
 Youtube
Youtube
Function creep.
It sounds like a virus and perhaps it is, although not the biological kind. Nor will it make your computer crash. Nothing so simple as that. It’s after your life.
Let's say you buy a camera and fill out the warranty card. You come to the part where it asks your age, whether you are married, how much you make, your hobbies and favorite magazines. You put down that the magazine you like best is something called The Sex Life of Turtles. Then you forget about it.
A year later you are applying for a job — plumber, painter, or poet, it doesn’t matter. Your prospective employer smiles across the vast expanse of his mahogany desk. He says, “So you’re interested in turtle sex, are you?” Friend, you’ve just been zapped by function creep: information compiled for one purpose being used for another.
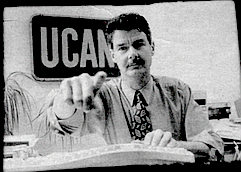
“There’s a lot of creeping going on these days,” says Barry Fraser, a San Diego telecommunications attorney who runs CyberCop, http://www.ucan.org, a Web site that collects complaints about consumer abuses on the Internet. “Information can creep either willingly or unwillingly. Consumers have no control anymore. Information given to one party will end up in the hands of second, third, and even fourth parties.”
Begun in August 1996, CyberCop is part of the Utility Consumers’ Action Network (UCAN), a nonprofit consumer-advocacy organization in San Diego County that has worked to help consumers on telecommunications, energy, computer, and privacy issues since 1984. In the spring of 1996, UCAN turned its attention to the Internet, and CyberCop was born.
“There’s no one else in the country doing what we’re doing,” says Fraser, “that has an on-line form. We wanted an interactive gripe site. We get complaints about consumer abuses every day.”
CyberCop not only takes complaints, it also provides a digest of these complaints, issues warnings about pyramid scams on the Internet, publishes a “Holding Cell" of Internet villains, and rates Internet service providers. As a way of attracting San Diegans to its Web site, CyberCop also provides a breakdown by community of the lowest gasoline prices and indicates where gas wars are taking place. Prices for a gallon of regular gasoline can differ by as much as SO cents.
But the main goal of CyberCop is to provide information to educate consumers.
“People need to learn the hazards,” says Fraser, “and to think before they type. The big concern is that if we use the Web as a marketplace, then we’re giving out private financial information on-line. Ifa merchant isn’t careful with how he stores credit card numbers, they can be stolen. There are very few safeguards as to what happens when you give out your credit card. You may not even be giving your credit card to a real business. It’s very easy to be anonymous on the Internet, to set up a fake name, fake address, and claim to be selling something that you’re not. Then you collect the money and credit card numbers, keep the Web site for a week or two, and disappear. Sites can come and go very quickly.”
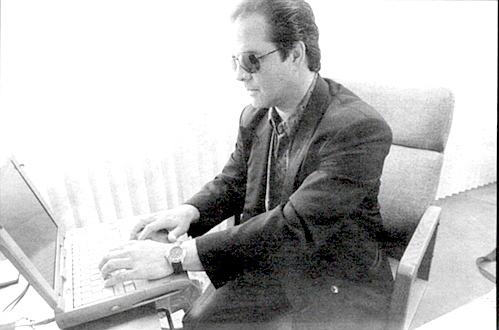
I was sitting with Barry Fraser in his small office filled with boxes of papers and computer equipment. A youthful 40, Fraser started out in TV journalism, worked for Channel 10, and still has his anchorman good looks. Ten years ago an interest in telecommunications led him to return to school for his master’s degree, which he followed with a law degree from the University of San Diego.
“I’ve always been a student of communications,” he says.
Fraser explains that as technology and the Internet continue to expand, there’s a greater struggle between those who want information and those who want to protect their privacy. But people can protect themselves by being careful about what information they give out. As an example, he calls up the search engine Big-foot on his computer and types in his name. On the screen appears a long list of Barry Frasers from around the country with their addresses and phone numbers. Next to Barry Fraser of CyberCop, however, no street address is given. “You see,” he tells me, “I don’t give it out.” But in front of each name is a button to call up a map site. Fraser clicks on the button, and the screen fills with a San Diego street map showing the neighborhood where Fraser lives, even though he had tried to keep his address private.
“Hmmm,” he says, attempting to modify his surprise. Then he adds, “Actually, I moved from there over a year ago.”
So the search engine presented information that Fraser had meant to keep private, but it was inaccurate information because it was a year out of date.
Is that an example of function creep? You bet.
Information is big business, and as the Internet gets bigger, so do the information vendors. One of the biggest is CDB Infotek in Santa Ana. For a subscriber fee, Infotek offers you information about anyone in the country. Criminal records, bankruptcies, tax liens, marriages, and divorces — Infotek’s information comes from public records, although some of those records may be more public than one might wish.
For example, its product Missing Links lets you search credit bureau header files with only a person’s name. The files themselves are protected by the federal Fair Credit Reporting Act, but the header files, which are the cover sheets, are public information.
And what might they contain?
Name, aliases, social security number, address, phone number (even if unlisted), birth date, median income, home value, demographic information on your house, how long you have lived there, previous addresses, and information on up to 30 of your neighbors.
Missing Links searches more than 542 million consumer credit bureau header files as well as over 146 million files from publishers’ mailing records, nationwide white pages directories, real property information, and household census data. Ten million additional records are added to or updated in the database each month.
And how much will a search cost?
Thirty-five smackers, and if Missing Links can’t find the person you’re looking for, you get your money back. And all of this is perfectly legal.
Information vendors like Infotek are designed for businesses seeking information about prospective employees, for landlords, rental agencies, private investigators, loan institutions— people without a lot of time or Internet expertise. Your average citizen with a few minutes to spare can just as easily pick up a copy of Naked in Cyberspace: How to Find Personal Information Online, published in June 1997 by the Pemberton Press.
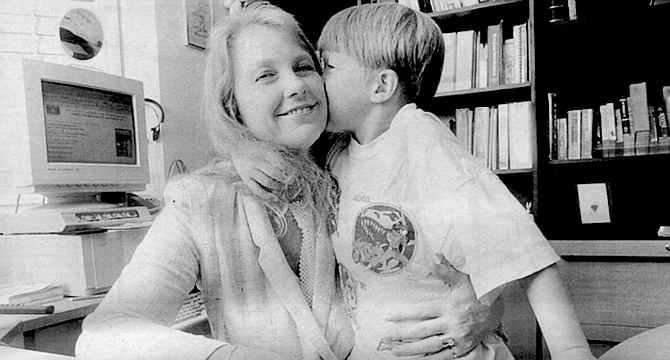
Written and compiled by Carole A. Lane of Oceanside, Naked in Cyberspace is ln personal records what the Encyclopedia Britannica Is to fads. And because new data is becoming available daily, the book has a Web site to keep its information current: www. onlineinc. com/pempress/ naked.
Ms. Lane is president of TechnoSearch in Oceanside, which does market research and competitive intelligence; that is, it investigates business and industry from a competitive standpoint, to see who’s there and just what the competition Is planning. She has also been hired by private investigators and public law enforcement agencies to locate people. Before opening TechnoSearch in 1993, Ms. Lane spent 11 years designing systems and databases in the medical and consumer credit industries.
As she writes at the beginning of her 500-page book, "In a few hours, sitting at my computer, beginning with no more than your name and address, I can find out what you do for a living, the names and ages of your spouse and children, what kind of car you drive, the value of your house and how much you pay in taxes on it. From what I learn about your job, your house, and the demographics of your neighborhood, I can make a good guess at your income. I can uncover that forgotten drug bust in college. In fact, if you are well-known or your name is sufficiently unusual, I can do all this without ever knowing your address. And, of course, if you become a skilled data searcher, familiar with the online resources available to us all, you will be able to learn much the same things about me, or almost anyone else who attracts your curiosity.”
But Ms. Lane is being modest. By studying her chapter on genealogical records, you can learn how to get the goods on the dearly departed going back to Noah’s ark. Military locators, watercraft ownership records. voter registration records, utility company records — wherever you have signed your name or made your mark, this information can be accessed by the casual browser.
“Fish and game licenses may seem fairly trivial as public records go,” writes Ms. Lane, “but they actually can be very useful. For example, someone who is hiding from creditors may not realize that a fishing trip can leave an automated paper trail that others can follow from across the country, leading them directly to his or her location.”
When I talk to Carole Lane on the phone, I tell her that I am shocked.
That’s nothing, she tells me. “Look at those kids who spout off in those youthnet news groups. Say a kid, a young anarchist, spouts off all sorts of garbage. All that stuff is archived. You can pull up every message a person has sent years later. It can affect a person in all sorts of ways. You don’t have control over where the information goes, and you don’t have control on whether the information is correct. In addition, most records exist in more than one place and can Ik accessed in many ways.”
Function creep, I tell myself .
“Supposedly a prospective employer can’t go back into your records more than seven years,” says Lane, “and they have to tell you why you were denied employment.” But often an employer won’t say how applicants were screened. Instead of saying exactly why you didn’t get the job, the employer will give you a pseudo reason, such as, “You don’t meet our present needs.”
I ask her about the accuracy of the records.
“Errors in personal records are one of the most common mistakes,” she tells me. “There are many studies on error ratios in credit records. Usually the person looking for the information only picks key identifiers and doesn’t bother making a complete match. We don’t have a unique identifier for individuals, something specific for them and no one else. At best, we have a person’s social security number, and that’s only a fairly good identifier since it lacks a photo and fingerprints. On the other hand, you will have a huge fight if you try to assign a unique identifier to each person, since it can be seen as an invasion of privacy. If there are no unique identifiers, then there will be errors and records that have merged badly. In many cases, records don’t have a tracking mechanism to show who pulled them. These records can be used by a prospective employer without any evidence that they have been used. And if you don’t know your record is being used, then you have no ability to correct it or do anything about it.”
So I go out in search of someone who has been the victim of such a mistake and turn up Ron Dean, who lives in Vista. Ron has a twin brother who is currently in prison for his third felony conviction. Ron himself doesn’t have a criminal record. Both men are 57, have similar backgrounds, and have the same initials — R.W. Dean. Their social security numbers differ by only one digit. And, of course, their mother’s maiden name— so important to banks and credit card companies — is identical. This has led to problems. Once, Ron was turned down for a life insurance policy because of a felony conviction appearing on his record. It was his brother’s. Another time he was denied access to his savings account because his brother’s social security number was listed on the file. But these difficulties were quickly cleared up.
For 25 years, Ron Dean ran his own construction business, but an on-the-job injury to his elbow in 1990 brought that to a halt. Ron looked for work but couldn’t find anything. He took classes to learn how to become a computer repair technician and certified Novell administrator, but he still wasn’t able to get a job.
Ron blames it on the confusion between his brother’s records and his own.
“I know it’s interfering with my ability to get work,” he says. “Several managers have told me that I’m just what they’re looking for since I’ve got 30 years’ experience in the construction business. They say I’ve got the job for sure. Then I come back the next day or next week and I get turned down. Just last week [the end of May] Home Depot turned me down for a job, but they refused to say why. The manager said they used a service, but he refused to talk to me about it.”
A reference or look-up service would present a prospective employer with Ron Dean’s record.
“Another manager told me that when they ask for a background check, the only answer they get is a ‘clear’ or ‘not clear’ for hire. I got a ‘not clear,’ but the manager didn’t know why and there wasn’t any way for me to find out. Everywhere I go it’s the same, even for jobs paying six dollars an hour — gasoline stations, retail jobs. At first everything seems fine, then it falls through.”
(Certainly it’s not surprising that Ron Dean’s records should occasionally be confused with his brother’s. 'The problem is that it seems impossible to check these records to discover if they are accurate. It’s impossible for him to find out if there is a mix-up or not. If a prospective employer used an investigative agency, then that agency is obliged to let the applicant know that he or she is being investigated and to give the applicant a copy of the report. But the law distinguishes between an investigative agency and a data bank, which may call itself just a collector of information and not an investigator. The data bank need not notify the applicant that it has supplied information. If the applicant demands to see the information, then the information will be released, but in order for that to happen the applicant has to know that a data bank has been used.
The difficulty, says David Brown, a lawyer in Downey whom Ron consulted, is that a prospective employer will try to avoid future problems by telling the applicant that he doesn’t meet their needs or that the job has been filed. In Ron Dean’s case, what a lawyer must do is ask if any service was used. The employer is legally obliged to tell the truth, and if a service was used, to supply a copy of the report.
“An employer has the right to go to any legitimate source and ask, ‘What kind of information do you guys have?’ ” Brown tells me. “But there’s a fine balance between how much a service can dig to get the information and how far they can go without invading a person’s privacy. In this day and age, computers arc making more problems in these areas — it’s easier to get information and there may be more mistakes.”
'There are many cases like Ron Dean’s where mistakes have been made and one person has been confused with another. Usually, the people concerned don’t know about the mistake until a problem arises. But once the mistakes become obvious, they can sometimes be cleared up. Still, they are caused by information collected for one purpose being used for another: function creep.
A greater problem is when the information is used to commit a crime, such as identity theft.
Grace, who lives in San Diego and asked that her last name not be used, was woken up by the San Diego police at 5:00 a.m. in December 1995 to be told that the police in Ontario, California, had arrested a woman who had bought a car with a credit card belonging to Grace’s daughter Klaine. Somehow the woman had gotten information about Klaine when Elaine went to the Department of Motor Vehicles in San Diego to change her address. Using KJaine’s name and social security number, the woman applied for a number of credit cards, then went to the post office and filed a change of address form saying that Elaine had moved to Ontario. Once the woman had the credit cards, she bought a car, tires, other merchandise, and made thousands of dollars’ worth of long-distance calls in Elaine’s name.
All of this came out after Elaine, who was 24, and her mother contacted the police in Ontario. By law, Elaine was only responsible for the first $50 on the credit cards, but she still had to clear up the mess, which meant contacting the credit card companies and checking her credit reports. Police said that the arrested woman had also gotten credit cards in the names of five other women, all about the same age.
“If this woman hadn’t been arrested,” Grace tells me, “it would have been much worse. It was a nightmare anyway. These things happen slowly, and so stuff might still turn up. For instance, just this past January when we thought this was over, my daughter’s car insurance was canceled. It turned out that this person had gotten a traffic ticket and used my daughter’s name. So we had to go up to Ontario and my daughter had to appear before the judge to show she wasn’t the person who had gotten the ticket. All of this took a huge amount of time.”
The ease with which credit cards can be obtained, coupled with the card companies’ superficial checking of information, has led to an increasing number of crimes.
Last October, Priscilla Murphy, a special education teacher in the Grossmont Union High School District, was called from class to take a telephone call. A woman from Avco Financial Services in Stockton wanted to know if Murphy had just ordered a houseload of furniture. Murphy had not.
Murphy acted quickly and contacted the police. Eventually she learned that three women — two in San Diego and one in Stockton — had obtained Murphy’s social security number and birth date. With that information they had applied for credit cards by mail and had opened 30 accounts—K Tenney, MacVs, Home Depot, AT&T, and many others. These cards were not sent to Murphy’s home but to the homes of the thieves, who have since been arrested.
“I’ve no idea how they got this information,” Murphy says. “Recently, I had to refinance my house and maybe some of that information got out. I had to go through an endless process with all these creditors to prove I was me. I had to make copies of my driver’s license, my phone bill, to fill out affidavits and send them all over the place. It was a real pain in the butt trying to clear it up. These people didn’t have my driver’s license or even my mother’s maiden name, but the burden of proof was still on me. I can’t tell you how angry I am that it was so easy to happen. And it’s not finished. There’s an account with a cellular phone company that I still can’t close. If this woman from Avco hadn’t called me, it would have been far, far worse. None of these accounts had gotten to the point where they were delinquent. I’d say it’s taken at least 80 hours to clear it up. I had to be bothered at work and kept being called from class. And it’s still going on. Just last week [end of May) I was called about a Target account that had recently been opened, even though an alert had been placed on my credit report warning of possible fraud and that they should double check before opening an account. I haven't applied for credit since this happened. What am I going to do if I want to get a loan or to buy a car? I used to be a real civil libertarian, but now I want my thumbprint on all my credit cards and that goes against everything I used to believe. It’s all a big joke, but it’s the little guy who pays the price. I really felt violated.”
What Priscilla Murphy and Grace don’t realize is that it’s unnecessary for thieves to steal compromising scraps of paper that might have been left at a bank or the Department of Motor Vehicles. Nor would the thieves need to pry through their trash — dumpster diving, it’s called. they would only need a copy of Carole line’s Naked in Cyberspace, and the information, including their driver’s license numbers and their mothers’ maiden names, could have been retrieved from the Internet. And this is because the technology is expanding far faster than the laws that might protect us from this technology.
Barry at CyberCop spoke of the ease with which information could be obtained and how easily it could be used for criminal purposes. “It’s surprising,” he says, “that there’s not a lot more of this going on.
The potential for crime is frightening, and I’m afraid that someday there’ll be an explosion of identity theft and people won’t be able to do anything about it.”
“All our identification is old-fashioned,” explains Gregory A. Estevane, a private investigator and attorney who is CEO of Professional Investigations, Inc. in San Diego and who has handled identity-theft cases and identity searches. “Identity issues are cropping up more and more. Someone can’t get a job and they feel there might be inaccuracies in the database used by the prospective employer. We’ve worked on that. Or someone calls and says that someone’s been using a credit card that’s in their name and they can’t get the police to help. We’ve worked on that too. And there are lots of gray areas where fake IDs are being used.
“People say it’s dangerous that all this information is available, and they want to regulate it. I think that would be terrible.
The government is trying to restrict information, but it’s going out more and more. The Internet really scares them. The thing is that the information is already out there. It’s too late to shut it down. You can get social security numbers off traffic tickets and marriage and divorce records. It’s all available and you can’t restrict it. Criminals dumpster dive. Computer hacking is an electronic form of dumpster diving. Personally, I feel that the more information that’s available, then the more freedoms we’ll have. Privacy rights as an issue will just get blown away, and I think that’s good. Information should be even more readily available. Everybody should have access to everything except credit records.”
Estevane believes that instead of restricting information, we should use the technology to make identifications more specific, that fingerprint and retinal scans and other technologies should be used. “We’ll eventually evolve to the point where technologY itself will be able to protect us."
But in the meantime we’re in an in-between period and people, says Estevane, are innocent and ignorant. “They don’t know how to protect themselves. They should shred all their trash and be far more careful with their pieces of identification.”
The man who deals with identity-theft cases in the San Diego Police Department is Detective Gene Bardot, who is part of the 16-man financial-crimes unit.
“I’ve been doing this seven years,” he tells me. “When I first started out, identity theft was rare. Now it’s increased exponentially. The three credit reporting agencies created their own fraud departments in 1992, and they each started out getting about 900 calls a day. Now their calls are about 2000 per day. We’re not finding much involvement with computers, but that’s bound to increase."
I ask Bardot what the credit card companies are doing about identity theft.
“The business or credit card company will write off the loss or factor the debt into their operating expenses, but you’re on the hook. Say somebody’s been using your name to buy all sorts of stuff — the credit card company will land on you and you’ll have to spend an inordinate amount of time playing defense. I’ve talked to attorneys whose clients have been hammered for years. Some people will have to deal with this all their lives, and a lot of the companies won’t even do a credit check to see if these people are having a problem or have flagged their accounts. Time is money, and a lot of these companies feel that to check every application to make sure there’s no fraud would take too much time. They do blind applications. They send off lots of open accounts and they know that some will be used fraudulently, but dealing with that is cheaper than checking every application in the first place. It’s a real problem, and the corporations aren’t taking very aggressive steps to stop it. There needs to be government regulation to make the businesses more responsible on how they handle their information.”
I ask Bardot what can be done.
“If a company’s going to take an application over the phone, then the legislature should deal with that to create safeguards. But if you walk into a place, like a finance company, to open an account, then you should give your fingerprint. And a career criminal knows what that fingerprint is going to do. It’ll stop him in his tracks.”
I ask Bardot what sort of people get involved with identity theft.
“The people who do this kind of stuff run the gamut from first-time crook to career criminal —a person can do this and be invisible. They can get a couple of other people to help them make the calls, and by the time it becomes public six months down the line, they’ve already disappeared. I could just take cash advances from an ATM machine or employ people to do it for me. Even if there’s a camera over the machine, I could disguise myself. The penalties for this stuff can be laughable. They’re just restitution, maybe some local jail time. Thieves can make big money doing a number of different cards, and we may only catch them on a little hit of the scam. Though it’s considered a felony, it’s not treated as one. It’s treated as a white-collar crime in which no one gets hurt, even though the guy whose name is being used can spend years trying to clear it up. That in itself is rather repulsive — the business and credit card companies make it your responsibility. They created the problem by being negligent, and you’ve got to deal with it.
“What would help would be for the person who’s opening the account to give their fingerprint. MasterCard is running a pilot program using a 'smart card,’ which has a microchip inside it with your thumbprint. The merchant has a machine that can read the card — by 2005, 2006 it will be universal on all cards. And you need to make sure you tear up the stuff with financial information into pieces that can’t be read. As it stands now, your trash is fair game. Once you put it on the curb, it’s no longer yours. There’s a lot of dumpster diving around financial institutions, car dealerships, and banks. We’re dealing with a case now where a company changed their checks and threw out thousands of their old ones without destroying them. Now they’re resurfacing all over the place. You’ve got to destroy all your financial information when you throw it out.”
Los Angeles is the capital of credit card fraud in the United States, and it’s also the capital of counterfeit money. I talk to Paul Edholm, a detective in the Beverly HiUs Buiko Forgery Unit who has had a 29-year career in law enforcement.
“As technology increases, the technology for the criminal increases,” Edholm explains. “They can improve the way they steal money. They can steal it better. For instance, it’s real easy for counterfeiters. They only need a scanner and safety paper for making checks. As for credit card forgers, with about 600 dollars’ worth of equipment you can start making your own cards with a mag stripe on the back. These guys try it out first at a gas station getting a buck's worth of gas. If it works there, then they take it to a store.”
I ask Edholm if he is having more credit card cases than five years ago.
“What I’ve seen is that there’s all of a sudden more credit card numbers being stolen. It’s very easy to impersonate a cardholder and have stuff sent to a PO box or even to a vacant house. Most card companies now have investigative agencies working for them. It’s become a huge problem. Crooks can get the information in all sorts of ways, but their main method is through dumpster diving. You can get enough from someone’s trash to destroy their lives. As an experiment, I went through the trash of four people, and I found enough on three of them to absolutely ruin them.”
I ask what kind of criminal specializes in credit card fraud.
“Everybody engages in it; there’s not one particular type of criminal. There are guys who let it be known that they will pay 75 bucks to buy a card on the day it’s been stolen. Trash divers love to go to car dealerships and financial institutions. They can find all sorts of good stuff. Sometimes they use it themselves, and sometimes they sell it to other crooks. Some guys will pay people to trash dive for them and break into cars looking for cards. They let it be known that they’re paying for this. Then they hire mules or walkers who are the people who actually go out and commit the credit card fraud. The mules take the risk.”
And what happens to the crooks who get convicted?
“If it’s a first offense, these people will get a slap on the hand, maybe have to pay restitution. The second time they might get three months or be given an electronic monitor and have to call in regularly. The monitor wouldn’t stop them from engaging in more credit card fraud. The problem is that the prisons are already jammed with people who’ve committed violent crimes and three-time losers, so these people guilty of nonviolent crimes get off very easily, no matter how much money they’ve stolen.”
Will smart cards with fingerprints cut down on fraud?
“In Europe these smart cards are very popular. You can have your whole medical history on one of these cards. The problem is that these cards are very expensive and cost about $14 each, while the cards we have now cost 27 cents. The credit card companies don’t like that. Then you have all the machinery necessary to read the card, which is a whole additional expense. Visa, MasterCard, Diners Club, and American Express all have plans on what they want to do, but each company wants to do it differently, and they can’t get together and agree on a single method. These credit cards with thumbprints and magstripes can also be counterfeited, because we’ve found that the new driver’s licenses with the fingerprint were counterfeited within three weeks of being issued."
I ask Edholm what people can do to protect themselves.
“You should check your credit record at least once a year to make sure there’s nothing there that shouldn’t be there, and you should also flag your credit report that you require a certain number of forms of identification before any credit can be issued in your name. Beyond that, the merchants need to be educated as to what counterfeit driver’s licenses and credit cards look like and to make sure that they match the number on the receipt with the number on the card. I recommend that people get a shredder. I have a shredder at home. Before that, I tore up my mail and put half the bank numbers and credit card numbers in one trash can and half in another.”
Experts agree that it will be a very short time before credit card thieves begin to depend on the Internet for their information. Armed with books like Naked in Cyberspace, why should someone dig through the trash or break into cars? An enterprising thief can open all the accounts he or she would want while curled up in front of the fireplace with a laptop computer. .This isn’t to judge books like Naked in Cyberspace. As Gregory Estevane says, there’s no way to halt the flow of information, and it would be harmful to do so.
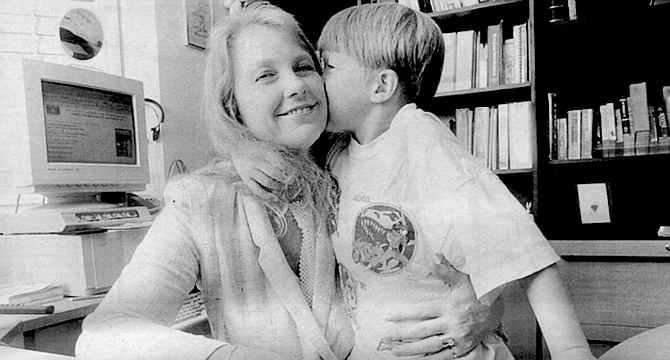
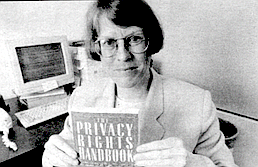
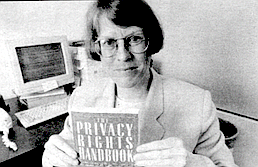
If this story has a hero, it must be Beth Givens, who is the director of San Diego’s Privacy Rights Clearinghouse. The clearinghouse is a sort of information vendor. It won’t solve your problems with horrors resulting from function creep—identify' theft, mixed-up records, junk mail tidal waves, telemarketing bullying, harassing phone calls, cyber-stalkers, wiretapping, eavesdropping, or a host of similar problems — but it will help you define the problem and tell you where to go to fix it.
Beth Givens is, as she tells me, “an information nut.” She has a passion for collecting information.
The clearinghouse began in 1992 with a grant awarded by the California Public Utilities Commission to the Center for Public Interest law at the University of San Diego for a consumer education project on privacy. The clearinghouse stayed at USD until last November and at its height had a staff of three and a project attorney. But grants come and grants go. Now the clearinghouse has moved to an office near the university, and its staff consists of Givens and two student workers. Under the umbrella of the Utility Consumers’ Action Network, the project has its own Web site: http://www.privacyrights.org. Givens works about 60 hours a week, and the phones always seem to be ringing.
“I really love the countryside around here,” Givens says, “and when I have the chance, I go up into the mountains.”
And it strikes me that a big reason for her fondness of the countryside is that it has no telephones, computers, Web sites, telemarketing, television — the vast spawn of electricity that is both our joy and torment and, for Givens, the foundation of her job and what she loves to do.
“Privacy Rights is a unique program,” says Givens. “We’re the only ones in the country doing this. We provide a road map for people to show them what they can do with their particular problem. For instance, many people don’t know that there’re regulatory boards that monitor various industries, and so we might direct them to that board.”
Givens’s background is in library science. Originally from Minnesota, she received her master’s at the University of Denver in the 1970s. Then she moved to Montana and had a position with the state library training librarians in how to use computers for library work. It was this that led to her fascination with computers and cyberspace. So she left Montana in 1985 to enroll in the Annenberg School in Los Angeles to obtain another master’s degree in communications management and telecommunications technology. She was also interested in the surrounding public policy issues and the effect on society of technical advances.
I tell her that with what she has learned she could become the world’s greatest cvbercrook.
“I was a student in the 70s,” she says simply, “and I guess a sense of social responsibility was drummed into me. If you have money, then you have the power to protect your privacy. Computers are becoming the main vehicles of intrusion into people’s privacy. And who is mostly victimized by this? People who hardly know the words to describe what’s going wrong with them. The Telecommunications Reform Act of 1996 enables all schools to have access to the Web and cyberspace, but schools in richer tax bases are more likely to have the necessary high-tech communications equipment. You have to be a pretty savvy consumer to be able to make use of the information that we provide, so we also seek to improve people's information skills.”
Givens goes around the country and lectures as well as testifying before congressional committees and at hearings held by the Federal Trade Commission. And she is part of California’s Joint legislative Task Force on Personal Information and Privacy chaired by Senator Steve Peace, D-El Cajon.
It is in these public arenas, Givens tells me, that the Privacy-Rights Clearinghouse “can have the most lasting impact.”
Givens and the small team that began the clearinghouse started by adopting a working definition of privacy: “The right to determine when, how, and to what extent information about us is communicated to others.” After that, they concentrated on how privacy could be protected.
It is Givens who introduces me to the term function creep. “It has to do with secondary usage. If private material is used for one purpose, then it may not be used for another purpose. If it slowly drifts off, then that’s function creep.”
The clearinghouse began producing publications, or fact sheets. The first was “Privacy Survival Guide: Flow to Take Control of Your Personal Information.”
“Every day most of us give away information about ourselves —sometimes knowingly and other times when we do not even realize it. You are your best privacy protector. Be Aware. Be Assertive. Be an Advocate."
The fact sheet discusses credit reports, medical histories, social security statements, driv ing records, mailing lusts, and a dozen other areas indicating how and why people should take control of their personal information.
And it warns people to he especially protective of their social security numbers, explaining when one needs to give it out and when one doesn’t.
Nineteen more fact sheets followed. At first the big issues were junk mail, telemarketing, and mistakes on people’s credit reports.
“Now the topics on the hotline,” says Givens, “are more concerned with identify theft — how thieves will take a person’s social security number and driver’s license and use them to order credit cards, which are sent to the thieves’ address. Fraud losses are now approaching three billion a year. A person’s social security number is the key to identity theft, and so people are increasingly upset by demands on it. Only the government can legally ask for your social security number, but increasingly it is being asked for by the private sector to open bank accounts and charge cards. You can refuse to give it, but then they can also refuse to give you an account.” Consequently, Fact Sheet Number 17 is “Coping with Identity theft: What to Do When an Impostor Strikes."
Another large issue addressed by the clearinghouse is workplace privacy.
“Usually a prospective employer,” says Givens, “wants the job applicant to sign a waiver which gives permission to get all the information on a person — medical records, financial and education records, and to talk to neighbors. The employers say they’re worried about negligent-hiring lawsuits and they need enough of a background check to know they'’re not hiring a psycho. But what constitutes a psycho? The prospective employer then has access to everything and can refuse to hire over some detail that has nothing to do with the job. And when the person tries to find out why he was turned down, he can’t learn anything. It’s like what happens in Kafka’s novel The Trial. ”
Those concerns resulted in Fact Sheet Number 16: “Employment Background Checks: A Jobseeker’s Guide.”
I ask Givens if the supporters of Privacy Rights Clearinghouse come from the political right or the left, but she says that the issue concerns the entire spectrum, from those who demand that government get off their backs to the American Civil Liberties Union. The fear is that if the information-vendor industry is not regulated, and if a person doesn’t have control or access to the information being circulated about him or her, then it’s possible to use nx>re and more of this information for social-control issues.
“They are already using driver’s license information to track down deadbeat parents,” says Givens. “What will be used next? Will they use your tax records? That’s function creep.”
As a result, even though Privacy Rights Clearinghouse was designed as a service for (Californians, it receives calls and e-mail from all over the country.
Now the 20 fact sheets of the Privacy Rights (Clearinghouse have been expanded into a book published this month by Avon — The Privacy Rights Handbook —which Givens wrote with Dale Fetherling, a San Diego journalist and the former San Diego bureau chief for the Los Angeles Times. The foreword was written by Ralph Nader.
“Each time you deposit or withdraw money at the ATM,” writes Givens, “visit the doctor, pay your mortgage, use a charge card, chat on the Internet, make a phone call, or do any of dozens of other routine tasks, you leave electronic ‘fingerprints.’ Nearly every quantifiable aspect of your life finds its way into a data bank somewhere. This staggering volume of information is sometimes scrutinized, other times ignored, and yet other times collected to be sold and perhaps resold again, all most likely without your knowledge.”
The book is full of chilling examples of thefts, intrusions, mix-ups, and confusions: “Laura, a physician in private practice, was puzzled about why she had trouble getting insurance for her office. Then she found out she’d been wrongly coded in a national medical records database as suffering from Alzheimer’s disease and having had heart disease."
It struck me as ironic that Naked in Cyberspace, which gives detailed instructions on how to find out about people from the Internet, and the Privacy Rights Handbook, which gives detailed instructions on how to protect yourself from such people, should be published within three months of each other and that their authors should live in San Diego.
These two areas, the information explosion and the privacy rights movement, seem to be rushing in opposite directions as the technology develops. At the moment, it isn’t clear what will be possible on the Internet and it isn’t clear how excessive the intrusions on a person’s privacy may become. Because of this, Barry Fraser of CyberCop worries about attempts to regulate the Internet, since those very regulations may impede the Internet’s growth.
“Information vendors can become the biggest future problem,” Fraser tells me, “but eventually technology itself will provide solutions. Ideally, it should he a self-policing effort on the part of the merchants who want to protect the Internet and their businesses. I here’s a great potential to get even on the Web. If you’re having trouble with a company, you can build a grudge page and advertise it in order to put pressure against the company. Regulation may be necessary, but it should be the last resort. What we want is to educate consumers.” And that, he adds, is why Beth Givens is so important.
San Diego Detective Gene Bardot agrees. “Beth Givens provides a great service by creating public awareness,” he tells me. “Not everybody’s going to get the message, but the more people you have aware of what’s going on and what to look for, then the better off law enforcement is and the better off the citizen is. Because otherwise, this is going to go on and it’s getting worse.”
“I adore Beth Givens,” says the private investigator, Gregory Estevane. “Everything she does is great. Even though we’re on opposite sides of the fence, she gives you my name so you can talk to me.”
I ask Givens how she feels about Estevane’s belief that information should be more readily available than it already is.
“We can’t have a transparent society,” she says, meaning a society in which all information is available, “until we have a tolerant society. As long as a person can be judged for something he or she did as an adolescent, or did and has long paid for, then some information should be protected.” In the meantime, she adds, “I think the Internet will be used increasingly for identity theft.”
In order to curb identity theft, there has been a rush this summer to pass new legislation to protect the consumer. Arizona Republican John Kyl has introduced a Senate bill that, among other tilings makes iden-
tity theft crossing state lines a crime with punishment of a fine and imprisonment up to 15 years and that allows restitution to the victim.
Senator Diane Feinstein has introduced a Senate bill that would prohibit the commercial acquisition and distribution of social security numbers without the consent of their holders and would prohibit the use of the number for identification without consent. It also would prevent credit bureaus from providing credit header information.
In California, Assembly-member Kevin Murray, D-Los Angeles, introduced Assembly Bill 156, which would amend the penal code making identity theft a crime (the law is now against false impersonation) and wouId give victims the ability to get restitution. It also requires that a company granting credit to a person must verify at least three forms of identification. And it requires that only one address be used, rather than having one address on the application and another to which goods should be sent.
The bill was passed by the assembly without a single dissenting vote and has been sent on to the senate.
And in the senate. Senator Herschel Rosenthal, D-West Los Angeles, introduced a bill to allow California consumers to get one free credit report each year. It would allow consumers to put a freeze on their credit reports to keep them from being given to third parties without the consumer’s permission. 'lTie bill also tries to deal with the address problem — that if the credit card company gets an application with an address that is different from the one on file with the credit bureau, then the correct address needs to be deter-mined. This bill was recently defeated in the banking committee. Its sponsors say they will reintroduce it next year.
Although there is skepticism on the part of the authorities as to whether these steps will decrease identity theft, they form a beginning. At first there was concern that the credit card companies themselves would oppose these bills, since they would make the application process more expensive, but Givens says that at least so far the companies have remained on the sidelines.
In June, the Federal Trade Commission held hearings in Washington, at which Givens was invited to testify, concerning information databases, privacy on the Internet, and children’s privacy issues. Givens said that there are many examples of companies on the Internet questioning children in order to get information about their parents.
In the meantime, Senator Peace’s task force on personal information and privacy, with three senators, three assemblymen, and about 35 advisors, continues to meet. This summer it’s investigating use of public records and information vendors. In the fall, a final meeting will be held to pull together the different areas and begin writing a report to determine whether there should be further changes to California laws. But in the meantime, the technology continues to mushroom, while the people — good guys and bad guys, rich and poor — struggle to catch up.
According to Senator Peace “Every day those computers keep cranking out of our control, more information is absorbed, more mistakes are made, and the task of bringing things back under control Just gets bigger and bigger.”
Function creep.
— Stephen Dobyns
Stephen Dobyns has been a reporter for the Detroit News and is the author of nine volumes of poetry and 18 novels, the most recent The Church of Dead Girls (Henry Holt and Company).

Function creep.
It sounds like a virus and perhaps it is, although not the biological kind. Nor will it make your computer crash. Nothing so simple as that. It’s after your life.
Let's say you buy a camera and fill out the warranty card. You come to the part where it asks your age, whether you are married, how much you make, your hobbies and favorite magazines. You put down that the magazine you like best is something called The Sex Life of Turtles. Then you forget about it.
A year later you are applying for a job — plumber, painter, or poet, it doesn’t matter. Your prospective employer smiles across the vast expanse of his mahogany desk. He says, “So you’re interested in turtle sex, are you?” Friend, you’ve just been zapped by function creep: information compiled for one purpose being used for another.
“There’s a lot of creeping going on these days,” says Barry Fraser, a San Diego telecommunications attorney who runs CyberCop, http://www.ucan.org, a Web site that collects complaints about consumer abuses on the Internet. “Information can creep either willingly or unwillingly. Consumers have no control anymore. Information given to one party will end up in the hands of second, third, and even fourth parties.”
Begun in August 1996, CyberCop is part of the Utility Consumers’ Action Network (UCAN), a nonprofit consumer-advocacy organization in San Diego County that has worked to help consumers on telecommunications, energy, computer, and privacy issues since 1984. In the spring of 1996, UCAN turned its attention to the Internet, and CyberCop was born.
“There’s no one else in the country doing what we’re doing,” says Fraser, “that has an on-line form. We wanted an interactive gripe site. We get complaints about consumer abuses every day.”
CyberCop not only takes complaints, it also provides a digest of these complaints, issues warnings about pyramid scams on the Internet, publishes a “Holding Cell" of Internet villains, and rates Internet service providers. As a way of attracting San Diegans to its Web site, CyberCop also provides a breakdown by community of the lowest gasoline prices and indicates where gas wars are taking place. Prices for a gallon of regular gasoline can differ by as much as SO cents.
But the main goal of CyberCop is to provide information to educate consumers.
“People need to learn the hazards,” says Fraser, “and to think before they type. The big concern is that if we use the Web as a marketplace, then we’re giving out private financial information on-line. Ifa merchant isn’t careful with how he stores credit card numbers, they can be stolen. There are very few safeguards as to what happens when you give out your credit card. You may not even be giving your credit card to a real business. It’s very easy to be anonymous on the Internet, to set up a fake name, fake address, and claim to be selling something that you’re not. Then you collect the money and credit card numbers, keep the Web site for a week or two, and disappear. Sites can come and go very quickly.”
I was sitting with Barry Fraser in his small office filled with boxes of papers and computer equipment. A youthful 40, Fraser started out in TV journalism, worked for Channel 10, and still has his anchorman good looks. Ten years ago an interest in telecommunications led him to return to school for his master’s degree, which he followed with a law degree from the University of San Diego.
“I’ve always been a student of communications,” he says.
Fraser explains that as technology and the Internet continue to expand, there’s a greater struggle between those who want information and those who want to protect their privacy. But people can protect themselves by being careful about what information they give out. As an example, he calls up the search engine Big-foot on his computer and types in his name. On the screen appears a long list of Barry Frasers from around the country with their addresses and phone numbers. Next to Barry Fraser of CyberCop, however, no street address is given. “You see,” he tells me, “I don’t give it out.” But in front of each name is a button to call up a map site. Fraser clicks on the button, and the screen fills with a San Diego street map showing the neighborhood where Fraser lives, even though he had tried to keep his address private.
“Hmmm,” he says, attempting to modify his surprise. Then he adds, “Actually, I moved from there over a year ago.”
So the search engine presented information that Fraser had meant to keep private, but it was inaccurate information because it was a year out of date.
Is that an example of function creep? You bet.
Information is big business, and as the Internet gets bigger, so do the information vendors. One of the biggest is CDB Infotek in Santa Ana. For a subscriber fee, Infotek offers you information about anyone in the country. Criminal records, bankruptcies, tax liens, marriages, and divorces — Infotek’s information comes from public records, although some of those records may be more public than one might wish.
For example, its product Missing Links lets you search credit bureau header files with only a person’s name. The files themselves are protected by the federal Fair Credit Reporting Act, but the header files, which are the cover sheets, are public information.
And what might they contain?
Name, aliases, social security number, address, phone number (even if unlisted), birth date, median income, home value, demographic information on your house, how long you have lived there, previous addresses, and information on up to 30 of your neighbors.
Missing Links searches more than 542 million consumer credit bureau header files as well as over 146 million files from publishers’ mailing records, nationwide white pages directories, real property information, and household census data. Ten million additional records are added to or updated in the database each month.
And how much will a search cost?
Thirty-five smackers, and if Missing Links can’t find the person you’re looking for, you get your money back. And all of this is perfectly legal.
Information vendors like Infotek are designed for businesses seeking information about prospective employees, for landlords, rental agencies, private investigators, loan institutions— people without a lot of time or Internet expertise. Your average citizen with a few minutes to spare can just as easily pick up a copy of Naked in Cyberspace: How to Find Personal Information Online, published in June 1997 by the Pemberton Press.
Written and compiled by Carole A. Lane of Oceanside, Naked in Cyberspace is ln personal records what the Encyclopedia Britannica Is to fads. And because new data is becoming available daily, the book has a Web site to keep its information current: www. onlineinc. com/pempress/ naked.
Ms. Lane is president of TechnoSearch in Oceanside, which does market research and competitive intelligence; that is, it investigates business and industry from a competitive standpoint, to see who’s there and just what the competition Is planning. She has also been hired by private investigators and public law enforcement agencies to locate people. Before opening TechnoSearch in 1993, Ms. Lane spent 11 years designing systems and databases in the medical and consumer credit industries.
As she writes at the beginning of her 500-page book, "In a few hours, sitting at my computer, beginning with no more than your name and address, I can find out what you do for a living, the names and ages of your spouse and children, what kind of car you drive, the value of your house and how much you pay in taxes on it. From what I learn about your job, your house, and the demographics of your neighborhood, I can make a good guess at your income. I can uncover that forgotten drug bust in college. In fact, if you are well-known or your name is sufficiently unusual, I can do all this without ever knowing your address. And, of course, if you become a skilled data searcher, familiar with the online resources available to us all, you will be able to learn much the same things about me, or almost anyone else who attracts your curiosity.”
But Ms. Lane is being modest. By studying her chapter on genealogical records, you can learn how to get the goods on the dearly departed going back to Noah’s ark. Military locators, watercraft ownership records. voter registration records, utility company records — wherever you have signed your name or made your mark, this information can be accessed by the casual browser.
“Fish and game licenses may seem fairly trivial as public records go,” writes Ms. Lane, “but they actually can be very useful. For example, someone who is hiding from creditors may not realize that a fishing trip can leave an automated paper trail that others can follow from across the country, leading them directly to his or her location.”
When I talk to Carole Lane on the phone, I tell her that I am shocked.
That’s nothing, she tells me. “Look at those kids who spout off in those youthnet news groups. Say a kid, a young anarchist, spouts off all sorts of garbage. All that stuff is archived. You can pull up every message a person has sent years later. It can affect a person in all sorts of ways. You don’t have control over where the information goes, and you don’t have control on whether the information is correct. In addition, most records exist in more than one place and can Ik accessed in many ways.”
Function creep, I tell myself .
“Supposedly a prospective employer can’t go back into your records more than seven years,” says Lane, “and they have to tell you why you were denied employment.” But often an employer won’t say how applicants were screened. Instead of saying exactly why you didn’t get the job, the employer will give you a pseudo reason, such as, “You don’t meet our present needs.”
I ask her about the accuracy of the records.
“Errors in personal records are one of the most common mistakes,” she tells me. “There are many studies on error ratios in credit records. Usually the person looking for the information only picks key identifiers and doesn’t bother making a complete match. We don’t have a unique identifier for individuals, something specific for them and no one else. At best, we have a person’s social security number, and that’s only a fairly good identifier since it lacks a photo and fingerprints. On the other hand, you will have a huge fight if you try to assign a unique identifier to each person, since it can be seen as an invasion of privacy. If there are no unique identifiers, then there will be errors and records that have merged badly. In many cases, records don’t have a tracking mechanism to show who pulled them. These records can be used by a prospective employer without any evidence that they have been used. And if you don’t know your record is being used, then you have no ability to correct it or do anything about it.”
So I go out in search of someone who has been the victim of such a mistake and turn up Ron Dean, who lives in Vista. Ron has a twin brother who is currently in prison for his third felony conviction. Ron himself doesn’t have a criminal record. Both men are 57, have similar backgrounds, and have the same initials — R.W. Dean. Their social security numbers differ by only one digit. And, of course, their mother’s maiden name— so important to banks and credit card companies — is identical. This has led to problems. Once, Ron was turned down for a life insurance policy because of a felony conviction appearing on his record. It was his brother’s. Another time he was denied access to his savings account because his brother’s social security number was listed on the file. But these difficulties were quickly cleared up.
For 25 years, Ron Dean ran his own construction business, but an on-the-job injury to his elbow in 1990 brought that to a halt. Ron looked for work but couldn’t find anything. He took classes to learn how to become a computer repair technician and certified Novell administrator, but he still wasn’t able to get a job.
Ron blames it on the confusion between his brother’s records and his own.
“I know it’s interfering with my ability to get work,” he says. “Several managers have told me that I’m just what they’re looking for since I’ve got 30 years’ experience in the construction business. They say I’ve got the job for sure. Then I come back the next day or next week and I get turned down. Just last week [the end of May] Home Depot turned me down for a job, but they refused to say why. The manager said they used a service, but he refused to talk to me about it.”
A reference or look-up service would present a prospective employer with Ron Dean’s record.
“Another manager told me that when they ask for a background check, the only answer they get is a ‘clear’ or ‘not clear’ for hire. I got a ‘not clear,’ but the manager didn’t know why and there wasn’t any way for me to find out. Everywhere I go it’s the same, even for jobs paying six dollars an hour — gasoline stations, retail jobs. At first everything seems fine, then it falls through.”
(Certainly it’s not surprising that Ron Dean’s records should occasionally be confused with his brother’s. 'The problem is that it seems impossible to check these records to discover if they are accurate. It’s impossible for him to find out if there is a mix-up or not. If a prospective employer used an investigative agency, then that agency is obliged to let the applicant know that he or she is being investigated and to give the applicant a copy of the report. But the law distinguishes between an investigative agency and a data bank, which may call itself just a collector of information and not an investigator. The data bank need not notify the applicant that it has supplied information. If the applicant demands to see the information, then the information will be released, but in order for that to happen the applicant has to know that a data bank has been used.
The difficulty, says David Brown, a lawyer in Downey whom Ron consulted, is that a prospective employer will try to avoid future problems by telling the applicant that he doesn’t meet their needs or that the job has been filed. In Ron Dean’s case, what a lawyer must do is ask if any service was used. The employer is legally obliged to tell the truth, and if a service was used, to supply a copy of the report.
“An employer has the right to go to any legitimate source and ask, ‘What kind of information do you guys have?’ ” Brown tells me. “But there’s a fine balance between how much a service can dig to get the information and how far they can go without invading a person’s privacy. In this day and age, computers arc making more problems in these areas — it’s easier to get information and there may be more mistakes.”
'There are many cases like Ron Dean’s where mistakes have been made and one person has been confused with another. Usually, the people concerned don’t know about the mistake until a problem arises. But once the mistakes become obvious, they can sometimes be cleared up. Still, they are caused by information collected for one purpose being used for another: function creep.
A greater problem is when the information is used to commit a crime, such as identity theft.
Grace, who lives in San Diego and asked that her last name not be used, was woken up by the San Diego police at 5:00 a.m. in December 1995 to be told that the police in Ontario, California, had arrested a woman who had bought a car with a credit card belonging to Grace’s daughter Klaine. Somehow the woman had gotten information about Klaine when Elaine went to the Department of Motor Vehicles in San Diego to change her address. Using KJaine’s name and social security number, the woman applied for a number of credit cards, then went to the post office and filed a change of address form saying that Elaine had moved to Ontario. Once the woman had the credit cards, she bought a car, tires, other merchandise, and made thousands of dollars’ worth of long-distance calls in Elaine’s name.
All of this came out after Elaine, who was 24, and her mother contacted the police in Ontario. By law, Elaine was only responsible for the first $50 on the credit cards, but she still had to clear up the mess, which meant contacting the credit card companies and checking her credit reports. Police said that the arrested woman had also gotten credit cards in the names of five other women, all about the same age.
“If this woman hadn’t been arrested,” Grace tells me, “it would have been much worse. It was a nightmare anyway. These things happen slowly, and so stuff might still turn up. For instance, just this past January when we thought this was over, my daughter’s car insurance was canceled. It turned out that this person had gotten a traffic ticket and used my daughter’s name. So we had to go up to Ontario and my daughter had to appear before the judge to show she wasn’t the person who had gotten the ticket. All of this took a huge amount of time.”
The ease with which credit cards can be obtained, coupled with the card companies’ superficial checking of information, has led to an increasing number of crimes.
Last October, Priscilla Murphy, a special education teacher in the Grossmont Union High School District, was called from class to take a telephone call. A woman from Avco Financial Services in Stockton wanted to know if Murphy had just ordered a houseload of furniture. Murphy had not.
Murphy acted quickly and contacted the police. Eventually she learned that three women — two in San Diego and one in Stockton — had obtained Murphy’s social security number and birth date. With that information they had applied for credit cards by mail and had opened 30 accounts—K Tenney, MacVs, Home Depot, AT&T, and many others. These cards were not sent to Murphy’s home but to the homes of the thieves, who have since been arrested.
“I’ve no idea how they got this information,” Murphy says. “Recently, I had to refinance my house and maybe some of that information got out. I had to go through an endless process with all these creditors to prove I was me. I had to make copies of my driver’s license, my phone bill, to fill out affidavits and send them all over the place. It was a real pain in the butt trying to clear it up. These people didn’t have my driver’s license or even my mother’s maiden name, but the burden of proof was still on me. I can’t tell you how angry I am that it was so easy to happen. And it’s not finished. There’s an account with a cellular phone company that I still can’t close. If this woman from Avco hadn’t called me, it would have been far, far worse. None of these accounts had gotten to the point where they were delinquent. I’d say it’s taken at least 80 hours to clear it up. I had to be bothered at work and kept being called from class. And it’s still going on. Just last week [end of May) I was called about a Target account that had recently been opened, even though an alert had been placed on my credit report warning of possible fraud and that they should double check before opening an account. I haven't applied for credit since this happened. What am I going to do if I want to get a loan or to buy a car? I used to be a real civil libertarian, but now I want my thumbprint on all my credit cards and that goes against everything I used to believe. It’s all a big joke, but it’s the little guy who pays the price. I really felt violated.”
What Priscilla Murphy and Grace don’t realize is that it’s unnecessary for thieves to steal compromising scraps of paper that might have been left at a bank or the Department of Motor Vehicles. Nor would the thieves need to pry through their trash — dumpster diving, it’s called. they would only need a copy of Carole line’s Naked in Cyberspace, and the information, including their driver’s license numbers and their mothers’ maiden names, could have been retrieved from the Internet. And this is because the technology is expanding far faster than the laws that might protect us from this technology.
Barry at CyberCop spoke of the ease with which information could be obtained and how easily it could be used for criminal purposes. “It’s surprising,” he says, “that there’s not a lot more of this going on.
The potential for crime is frightening, and I’m afraid that someday there’ll be an explosion of identity theft and people won’t be able to do anything about it.”
“All our identification is old-fashioned,” explains Gregory A. Estevane, a private investigator and attorney who is CEO of Professional Investigations, Inc. in San Diego and who has handled identity-theft cases and identity searches. “Identity issues are cropping up more and more. Someone can’t get a job and they feel there might be inaccuracies in the database used by the prospective employer. We’ve worked on that. Or someone calls and says that someone’s been using a credit card that’s in their name and they can’t get the police to help. We’ve worked on that too. And there are lots of gray areas where fake IDs are being used.
“People say it’s dangerous that all this information is available, and they want to regulate it. I think that would be terrible.
The government is trying to restrict information, but it’s going out more and more. The Internet really scares them. The thing is that the information is already out there. It’s too late to shut it down. You can get social security numbers off traffic tickets and marriage and divorce records. It’s all available and you can’t restrict it. Criminals dumpster dive. Computer hacking is an electronic form of dumpster diving. Personally, I feel that the more information that’s available, then the more freedoms we’ll have. Privacy rights as an issue will just get blown away, and I think that’s good. Information should be even more readily available. Everybody should have access to everything except credit records.”
Estevane believes that instead of restricting information, we should use the technology to make identifications more specific, that fingerprint and retinal scans and other technologies should be used. “We’ll eventually evolve to the point where technologY itself will be able to protect us."
But in the meantime we’re in an in-between period and people, says Estevane, are innocent and ignorant. “They don’t know how to protect themselves. They should shred all their trash and be far more careful with their pieces of identification.”
The man who deals with identity-theft cases in the San Diego Police Department is Detective Gene Bardot, who is part of the 16-man financial-crimes unit.
“I’ve been doing this seven years,” he tells me. “When I first started out, identity theft was rare. Now it’s increased exponentially. The three credit reporting agencies created their own fraud departments in 1992, and they each started out getting about 900 calls a day. Now their calls are about 2000 per day. We’re not finding much involvement with computers, but that’s bound to increase."
I ask Bardot what the credit card companies are doing about identity theft.
“The business or credit card company will write off the loss or factor the debt into their operating expenses, but you’re on the hook. Say somebody’s been using your name to buy all sorts of stuff — the credit card company will land on you and you’ll have to spend an inordinate amount of time playing defense. I’ve talked to attorneys whose clients have been hammered for years. Some people will have to deal with this all their lives, and a lot of the companies won’t even do a credit check to see if these people are having a problem or have flagged their accounts. Time is money, and a lot of these companies feel that to check every application to make sure there’s no fraud would take too much time. They do blind applications. They send off lots of open accounts and they know that some will be used fraudulently, but dealing with that is cheaper than checking every application in the first place. It’s a real problem, and the corporations aren’t taking very aggressive steps to stop it. There needs to be government regulation to make the businesses more responsible on how they handle their information.”
I ask Bardot what can be done.
“If a company’s going to take an application over the phone, then the legislature should deal with that to create safeguards. But if you walk into a place, like a finance company, to open an account, then you should give your fingerprint. And a career criminal knows what that fingerprint is going to do. It’ll stop him in his tracks.”
I ask Bardot what sort of people get involved with identity theft.
“The people who do this kind of stuff run the gamut from first-time crook to career criminal —a person can do this and be invisible. They can get a couple of other people to help them make the calls, and by the time it becomes public six months down the line, they’ve already disappeared. I could just take cash advances from an ATM machine or employ people to do it for me. Even if there’s a camera over the machine, I could disguise myself. The penalties for this stuff can be laughable. They’re just restitution, maybe some local jail time. Thieves can make big money doing a number of different cards, and we may only catch them on a little hit of the scam. Though it’s considered a felony, it’s not treated as one. It’s treated as a white-collar crime in which no one gets hurt, even though the guy whose name is being used can spend years trying to clear it up. That in itself is rather repulsive — the business and credit card companies make it your responsibility. They created the problem by being negligent, and you’ve got to deal with it.
“What would help would be for the person who’s opening the account to give their fingerprint. MasterCard is running a pilot program using a 'smart card,’ which has a microchip inside it with your thumbprint. The merchant has a machine that can read the card — by 2005, 2006 it will be universal on all cards. And you need to make sure you tear up the stuff with financial information into pieces that can’t be read. As it stands now, your trash is fair game. Once you put it on the curb, it’s no longer yours. There’s a lot of dumpster diving around financial institutions, car dealerships, and banks. We’re dealing with a case now where a company changed their checks and threw out thousands of their old ones without destroying them. Now they’re resurfacing all over the place. You’ve got to destroy all your financial information when you throw it out.”
Los Angeles is the capital of credit card fraud in the United States, and it’s also the capital of counterfeit money. I talk to Paul Edholm, a detective in the Beverly HiUs Buiko Forgery Unit who has had a 29-year career in law enforcement.
“As technology increases, the technology for the criminal increases,” Edholm explains. “They can improve the way they steal money. They can steal it better. For instance, it’s real easy for counterfeiters. They only need a scanner and safety paper for making checks. As for credit card forgers, with about 600 dollars’ worth of equipment you can start making your own cards with a mag stripe on the back. These guys try it out first at a gas station getting a buck's worth of gas. If it works there, then they take it to a store.”
I ask Edholm if he is having more credit card cases than five years ago.
“What I’ve seen is that there’s all of a sudden more credit card numbers being stolen. It’s very easy to impersonate a cardholder and have stuff sent to a PO box or even to a vacant house. Most card companies now have investigative agencies working for them. It’s become a huge problem. Crooks can get the information in all sorts of ways, but their main method is through dumpster diving. You can get enough from someone’s trash to destroy their lives. As an experiment, I went through the trash of four people, and I found enough on three of them to absolutely ruin them.”
I ask what kind of criminal specializes in credit card fraud.
“Everybody engages in it; there’s not one particular type of criminal. There are guys who let it be known that they will pay 75 bucks to buy a card on the day it’s been stolen. Trash divers love to go to car dealerships and financial institutions. They can find all sorts of good stuff. Sometimes they use it themselves, and sometimes they sell it to other crooks. Some guys will pay people to trash dive for them and break into cars looking for cards. They let it be known that they’re paying for this. Then they hire mules or walkers who are the people who actually go out and commit the credit card fraud. The mules take the risk.”
And what happens to the crooks who get convicted?
“If it’s a first offense, these people will get a slap on the hand, maybe have to pay restitution. The second time they might get three months or be given an electronic monitor and have to call in regularly. The monitor wouldn’t stop them from engaging in more credit card fraud. The problem is that the prisons are already jammed with people who’ve committed violent crimes and three-time losers, so these people guilty of nonviolent crimes get off very easily, no matter how much money they’ve stolen.”
Will smart cards with fingerprints cut down on fraud?
“In Europe these smart cards are very popular. You can have your whole medical history on one of these cards. The problem is that these cards are very expensive and cost about $14 each, while the cards we have now cost 27 cents. The credit card companies don’t like that. Then you have all the machinery necessary to read the card, which is a whole additional expense. Visa, MasterCard, Diners Club, and American Express all have plans on what they want to do, but each company wants to do it differently, and they can’t get together and agree on a single method. These credit cards with thumbprints and magstripes can also be counterfeited, because we’ve found that the new driver’s licenses with the fingerprint were counterfeited within three weeks of being issued."
I ask Edholm what people can do to protect themselves.
“You should check your credit record at least once a year to make sure there’s nothing there that shouldn’t be there, and you should also flag your credit report that you require a certain number of forms of identification before any credit can be issued in your name. Beyond that, the merchants need to be educated as to what counterfeit driver’s licenses and credit cards look like and to make sure that they match the number on the receipt with the number on the card. I recommend that people get a shredder. I have a shredder at home. Before that, I tore up my mail and put half the bank numbers and credit card numbers in one trash can and half in another.”
Experts agree that it will be a very short time before credit card thieves begin to depend on the Internet for their information. Armed with books like Naked in Cyberspace, why should someone dig through the trash or break into cars? An enterprising thief can open all the accounts he or she would want while curled up in front of the fireplace with a laptop computer. .This isn’t to judge books like Naked in Cyberspace. As Gregory Estevane says, there’s no way to halt the flow of information, and it would be harmful to do so.
If this story has a hero, it must be Beth Givens, who is the director of San Diego’s Privacy Rights Clearinghouse. The clearinghouse is a sort of information vendor. It won’t solve your problems with horrors resulting from function creep—identify' theft, mixed-up records, junk mail tidal waves, telemarketing bullying, harassing phone calls, cyber-stalkers, wiretapping, eavesdropping, or a host of similar problems — but it will help you define the problem and tell you where to go to fix it.
Beth Givens is, as she tells me, “an information nut.” She has a passion for collecting information.
The clearinghouse began in 1992 with a grant awarded by the California Public Utilities Commission to the Center for Public Interest law at the University of San Diego for a consumer education project on privacy. The clearinghouse stayed at USD until last November and at its height had a staff of three and a project attorney. But grants come and grants go. Now the clearinghouse has moved to an office near the university, and its staff consists of Givens and two student workers. Under the umbrella of the Utility Consumers’ Action Network, the project has its own Web site: http://www.privacyrights.org. Givens works about 60 hours a week, and the phones always seem to be ringing.
“I really love the countryside around here,” Givens says, “and when I have the chance, I go up into the mountains.”
And it strikes me that a big reason for her fondness of the countryside is that it has no telephones, computers, Web sites, telemarketing, television — the vast spawn of electricity that is both our joy and torment and, for Givens, the foundation of her job and what she loves to do.
“Privacy Rights is a unique program,” says Givens. “We’re the only ones in the country doing this. We provide a road map for people to show them what they can do with their particular problem. For instance, many people don’t know that there’re regulatory boards that monitor various industries, and so we might direct them to that board.”
Givens’s background is in library science. Originally from Minnesota, she received her master’s at the University of Denver in the 1970s. Then she moved to Montana and had a position with the state library training librarians in how to use computers for library work. It was this that led to her fascination with computers and cyberspace. So she left Montana in 1985 to enroll in the Annenberg School in Los Angeles to obtain another master’s degree in communications management and telecommunications technology. She was also interested in the surrounding public policy issues and the effect on society of technical advances.
I tell her that with what she has learned she could become the world’s greatest cvbercrook.
“I was a student in the 70s,” she says simply, “and I guess a sense of social responsibility was drummed into me. If you have money, then you have the power to protect your privacy. Computers are becoming the main vehicles of intrusion into people’s privacy. And who is mostly victimized by this? People who hardly know the words to describe what’s going wrong with them. The Telecommunications Reform Act of 1996 enables all schools to have access to the Web and cyberspace, but schools in richer tax bases are more likely to have the necessary high-tech communications equipment. You have to be a pretty savvy consumer to be able to make use of the information that we provide, so we also seek to improve people's information skills.”
Givens goes around the country and lectures as well as testifying before congressional committees and at hearings held by the Federal Trade Commission. And she is part of California’s Joint legislative Task Force on Personal Information and Privacy chaired by Senator Steve Peace, D-El Cajon.
It is in these public arenas, Givens tells me, that the Privacy-Rights Clearinghouse “can have the most lasting impact.”
Givens and the small team that began the clearinghouse started by adopting a working definition of privacy: “The right to determine when, how, and to what extent information about us is communicated to others.” After that, they concentrated on how privacy could be protected.
It is Givens who introduces me to the term function creep. “It has to do with secondary usage. If private material is used for one purpose, then it may not be used for another purpose. If it slowly drifts off, then that’s function creep.”
The clearinghouse began producing publications, or fact sheets. The first was “Privacy Survival Guide: Flow to Take Control of Your Personal Information.”
“Every day most of us give away information about ourselves —sometimes knowingly and other times when we do not even realize it. You are your best privacy protector. Be Aware. Be Assertive. Be an Advocate."
The fact sheet discusses credit reports, medical histories, social security statements, driv ing records, mailing lusts, and a dozen other areas indicating how and why people should take control of their personal information.
And it warns people to he especially protective of their social security numbers, explaining when one needs to give it out and when one doesn’t.
Nineteen more fact sheets followed. At first the big issues were junk mail, telemarketing, and mistakes on people’s credit reports.
“Now the topics on the hotline,” says Givens, “are more concerned with identify theft — how thieves will take a person’s social security number and driver’s license and use them to order credit cards, which are sent to the thieves’ address. Fraud losses are now approaching three billion a year. A person’s social security number is the key to identity theft, and so people are increasingly upset by demands on it. Only the government can legally ask for your social security number, but increasingly it is being asked for by the private sector to open bank accounts and charge cards. You can refuse to give it, but then they can also refuse to give you an account.” Consequently, Fact Sheet Number 17 is “Coping with Identity theft: What to Do When an Impostor Strikes."
Another large issue addressed by the clearinghouse is workplace privacy.
“Usually a prospective employer,” says Givens, “wants the job applicant to sign a waiver which gives permission to get all the information on a person — medical records, financial and education records, and to talk to neighbors. The employers say they’re worried about negligent-hiring lawsuits and they need enough of a background check to know they'’re not hiring a psycho. But what constitutes a psycho? The prospective employer then has access to everything and can refuse to hire over some detail that has nothing to do with the job. And when the person tries to find out why he was turned down, he can’t learn anything. It’s like what happens in Kafka’s novel The Trial. ”
Those concerns resulted in Fact Sheet Number 16: “Employment Background Checks: A Jobseeker’s Guide.”
I ask Givens if the supporters of Privacy Rights Clearinghouse come from the political right or the left, but she says that the issue concerns the entire spectrum, from those who demand that government get off their backs to the American Civil Liberties Union. The fear is that if the information-vendor industry is not regulated, and if a person doesn’t have control or access to the information being circulated about him or her, then it’s possible to use nx>re and more of this information for social-control issues.
“They are already using driver’s license information to track down deadbeat parents,” says Givens. “What will be used next? Will they use your tax records? That’s function creep.”
As a result, even though Privacy Rights Clearinghouse was designed as a service for (Californians, it receives calls and e-mail from all over the country.
Now the 20 fact sheets of the Privacy Rights (Clearinghouse have been expanded into a book published this month by Avon — The Privacy Rights Handbook —which Givens wrote with Dale Fetherling, a San Diego journalist and the former San Diego bureau chief for the Los Angeles Times. The foreword was written by Ralph Nader.
“Each time you deposit or withdraw money at the ATM,” writes Givens, “visit the doctor, pay your mortgage, use a charge card, chat on the Internet, make a phone call, or do any of dozens of other routine tasks, you leave electronic ‘fingerprints.’ Nearly every quantifiable aspect of your life finds its way into a data bank somewhere. This staggering volume of information is sometimes scrutinized, other times ignored, and yet other times collected to be sold and perhaps resold again, all most likely without your knowledge.”
The book is full of chilling examples of thefts, intrusions, mix-ups, and confusions: “Laura, a physician in private practice, was puzzled about why she had trouble getting insurance for her office. Then she found out she’d been wrongly coded in a national medical records database as suffering from Alzheimer’s disease and having had heart disease."
It struck me as ironic that Naked in Cyberspace, which gives detailed instructions on how to find out about people from the Internet, and the Privacy Rights Handbook, which gives detailed instructions on how to protect yourself from such people, should be published within three months of each other and that their authors should live in San Diego.
These two areas, the information explosion and the privacy rights movement, seem to be rushing in opposite directions as the technology develops. At the moment, it isn’t clear what will be possible on the Internet and it isn’t clear how excessive the intrusions on a person’s privacy may become. Because of this, Barry Fraser of CyberCop worries about attempts to regulate the Internet, since those very regulations may impede the Internet’s growth.
“Information vendors can become the biggest future problem,” Fraser tells me, “but eventually technology itself will provide solutions. Ideally, it should he a self-policing effort on the part of the merchants who want to protect the Internet and their businesses. I here’s a great potential to get even on the Web. If you’re having trouble with a company, you can build a grudge page and advertise it in order to put pressure against the company. Regulation may be necessary, but it should be the last resort. What we want is to educate consumers.” And that, he adds, is why Beth Givens is so important.
San Diego Detective Gene Bardot agrees. “Beth Givens provides a great service by creating public awareness,” he tells me. “Not everybody’s going to get the message, but the more people you have aware of what’s going on and what to look for, then the better off law enforcement is and the better off the citizen is. Because otherwise, this is going to go on and it’s getting worse.”
“I adore Beth Givens,” says the private investigator, Gregory Estevane. “Everything she does is great. Even though we’re on opposite sides of the fence, she gives you my name so you can talk to me.”
I ask Givens how she feels about Estevane’s belief that information should be more readily available than it already is.
“We can’t have a transparent society,” she says, meaning a society in which all information is available, “until we have a tolerant society. As long as a person can be judged for something he or she did as an adolescent, or did and has long paid for, then some information should be protected.” In the meantime, she adds, “I think the Internet will be used increasingly for identity theft.”
In order to curb identity theft, there has been a rush this summer to pass new legislation to protect the consumer. Arizona Republican John Kyl has introduced a Senate bill that, among other tilings makes iden-
tity theft crossing state lines a crime with punishment of a fine and imprisonment up to 15 years and that allows restitution to the victim.
Senator Diane Feinstein has introduced a Senate bill that would prohibit the commercial acquisition and distribution of social security numbers without the consent of their holders and would prohibit the use of the number for identification without consent. It also would prevent credit bureaus from providing credit header information.
In California, Assembly-member Kevin Murray, D-Los Angeles, introduced Assembly Bill 156, which would amend the penal code making identity theft a crime (the law is now against false impersonation) and wouId give victims the ability to get restitution. It also requires that a company granting credit to a person must verify at least three forms of identification. And it requires that only one address be used, rather than having one address on the application and another to which goods should be sent.
The bill was passed by the assembly without a single dissenting vote and has been sent on to the senate.
And in the senate. Senator Herschel Rosenthal, D-West Los Angeles, introduced a bill to allow California consumers to get one free credit report each year. It would allow consumers to put a freeze on their credit reports to keep them from being given to third parties without the consumer’s permission. 'lTie bill also tries to deal with the address problem — that if the credit card company gets an application with an address that is different from the one on file with the credit bureau, then the correct address needs to be deter-mined. This bill was recently defeated in the banking committee. Its sponsors say they will reintroduce it next year.
Although there is skepticism on the part of the authorities as to whether these steps will decrease identity theft, they form a beginning. At first there was concern that the credit card companies themselves would oppose these bills, since they would make the application process more expensive, but Givens says that at least so far the companies have remained on the sidelines.
In June, the Federal Trade Commission held hearings in Washington, at which Givens was invited to testify, concerning information databases, privacy on the Internet, and children’s privacy issues. Givens said that there are many examples of companies on the Internet questioning children in order to get information about their parents.
In the meantime, Senator Peace’s task force on personal information and privacy, with three senators, three assemblymen, and about 35 advisors, continues to meet. This summer it’s investigating use of public records and information vendors. In the fall, a final meeting will be held to pull together the different areas and begin writing a report to determine whether there should be further changes to California laws. But in the meantime, the technology continues to mushroom, while the people — good guys and bad guys, rich and poor — struggle to catch up.
According to Senator Peace “Every day those computers keep cranking out of our control, more information is absorbed, more mistakes are made, and the task of bringing things back under control Just gets bigger and bigger.”
Function creep.
— Stephen Dobyns
Stephen Dobyns has been a reporter for the Detroit News and is the author of nine volumes of poetry and 18 novels, the most recent The Church of Dead Girls (Henry Holt and Company).
Comments